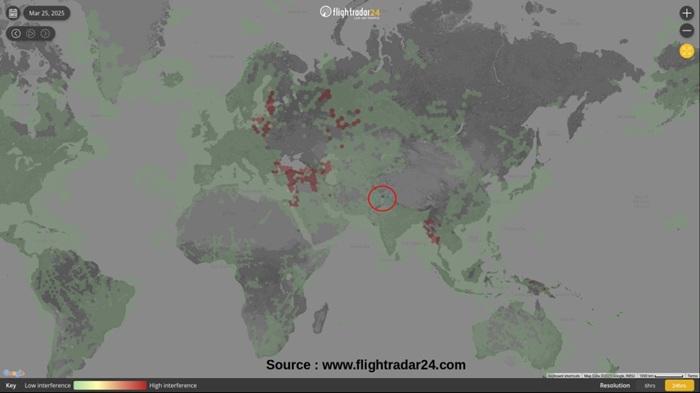
Recent media reports have highlighted the growing menace of GPS Spoofing across the world and its potential disastrous effects on a range of technical systems and utilities, especially aviation. This is especially worrisome when an increasing trend is observed near our borders. The Amritsar border has been discussed by the media and also in the Parliament. A map showing areas affected by frequent GPS Interference as of 25 Mar 2025, is shown below.
Generically, GPS (Navigation based on GNSS – Global Satellite Navigation System) is a Position, Navigation and Timing (PNT) reference system available openly for use by a vast range of services across the globe. It is based on using a constellation of satellites which while operating in different spatial planes enable PNT services on earth’s surface in coordination with a complex network of ground-based control station. This PNT information enables a range of technology solutions for transportation (human, vehicles, aircraft, ships etc.), communications (mobile phones, sat-phones, Internet etc.), finance, habitat management, disaster management, various scientific endeavours, military applications (land/air/sea/space/cyber) through over a vast ecosystem of GPS enabled devices.
Historically, GPS has been divided into a civil version (degraded precision with Selective Availability) and a military version (with higher precision). Technological advancements, large revenue potential and certain geo-political developments led to the removal of Selective Applicability mechanisms, providing high accuracy capability for civil usage. While the US GPS was the earliest system, the European Galileo, Russian Glonass, Chinese Beidou, Japanese Quasi Zenith Satellite System (QZSS) and Indian NAVIC are the newer and advanced options available to users. Contemporary PNT solutions also provide a capability to use multiple GPS options from different service providers, offering higher redundancy, resilience and accuracy.
As the GPS capability got integrated with the civil, military and other national capabilities, given the trajectory of conflicts in late 20th and 21st centuries, its weaponisation was an expected possibility. Accordingly, the Counter GPS technologies advanced at a rapid pace within the military domain. However, during the last decade advancements in Signals, Cyber and Software engineering domains have resulted in proliferation of mass-produced low-cost systems (like programmable Signal Generators, SDRs etc.) which can be used to manipulate GPS with ease, even by amateurs, enthusiast and hobbyists. The threat gets further amplified due to the fusion of Signal and Cyber technologies, seducing the Hacker community to apply their skill sets. GPS Manipulation capabilities are now increasingly available to both the State (with expensive and complex systems) and non-State actors (light weight / low-cost systems), with the latter not bound by any rules, ethics or norms. The State backed non-State actors offer an even more lethal combination with technological enablements of a State actor with no limitation modus-operandi of a non-State actor.
The GPS manipulation or spoofing broadly involves jamming the GPS signals, causing interference in the Signal flows or contaminating/falsifying the GPS data. The art of GPS Spoofing straddles the twin domains of Signals Processing and Cyber Offensive operations. Invariably, GPS spoofing commences with dominating the legitimate satellite signals available to the user with spurious signals with higher RF power. A more sophisticated endeavour involves triggering higher power GPS signals coupled with providing an apparently legitimate signal/content with contaminated data content, forcing the GPS user to get trapped into using the wrong signal/information.
GPS Manipulation can lead to some very serious consequences for civil navigation, disaster relief, supply chains, financial flows, military operations etc. As has been witnessed during the Russia-Ukraine and the West Asian conflicts, GPS Manipulation has impacted the outcome of military operations at both the tactical and strategic levels. An extreme case is that of a missile or an offensive drone with manipulated GPS attacking its own forces / infrastructure instead of attacking the adversary. A hospital vehicle or an air ambulance carrying a critical patient may end up being diverted, leading to loss of life. Malicious interference in GPS Data Streams can lead to collisions of airliners, ships or tankers leading to tragic loss of life and environmental disasters. Such an act committed by a non-State actor, a terrorist or an adversary intelligence agency during no-war situation can lead to a very complex threat scenario needing mitigation in multiple technology and policy dimensions.
India is saddled with a troublesome neighbourhood which impacts our national security during both peace and war time. While the Counter Technology options get factored in the war plans (which still encounter surprises), it is the peacetime intelligence offensive by our adversaries that needs to be addressed at the strategic level. This is bound to have a large impact footprint across the business of life and management of sovereignty. It is known that China, Pakistan and their proxies have a demonstrated capability to interfere with our Sovereign Signal Space, irrespective of their international and bilateral commitments. The problem gets further amplified when the capabilities like the GPS Manipulation gets exercised by a non-state actor with all the deniability options.
Given the magnitude of the threat, deploying Counter Measures at both the strategic/policy and tactical level is an inescapable necessity. It is known that the existing GPS framework is being augmented through integration of the Indian GNSS system and through terrestrial / augmented PNT network and Radio Navigation systems. This is in parallel with other policy and SOP related measures being undertaken in coordination with the affected users and international organizations like the ICAO. A terrestrial PNT network can also enable sovereign exclusivity and control over such services. However, the large impact space of the GPS Manipulation threat may make the current mitigation measures, in the space and ground segments, in-sufficient in the long term. This may require a more holistic approach on augmenting the existing PNT framework, integrating capabilities from other domains and building a new and more resilient infrastructure.
The long-term mitigation measures may include a potent threat detection infrastructure based on a persistent and resilient border area Signal monitoring and analysis capability at tactical and theater level. This capability while being traditionally part of the Sigint domain, can enhance detection of GPS Signal Interference and Manipulation over large time and space segments while geo-locating the source of such interference. Such Sigint devices need be unmanned/remotely-controlled, capable of undertaking immediate analysis and generating threat alerts at tactical levels, while sending the data back to a Command and Control center for strategic analysis using AI/ML driven Big-data systems. The characterization and geo-location of such signals can also lead to attribution and exposing the actor, especially those from across the border, besides mitigation.
The terrestrial PNT capability can be further enhanced through integration of the existing mobile communication and RF emission infrastructure, a technically proven solution. Needless to mention that these measures can hugely augment the dedicated PNT network, during both peace and war time.
The Indian industry and academia are more than capable of addressing the challenge as it will be futile to mitigate such a threat through foreign sourced solutions. Such imported systems can be technologically opaque with hidden back doors and are vulnerable to supply chain manipulations, something not desirable for a critical national capability such as the GPS PNT service.
(The paper is the author’s individual scholastic articulation. The author certifies that the article/paper is original in content, unpublished and it has not been submitted for publication/web upload elsewhere, and that the facts and figures quoted are duly referenced, as needed, and are believed to be correct). (The paper does not necessarily represent the organisational stance... More >>
Image Source: https://us.norton.com/content/dam/blogs/images/norton/am/gps-spoofing-hero.jpg










Post new comment